- Our Solutions
- Our Services
- ASSESS Cyber Risk and Maturity Assessment
- AWARE Cyber Security Awareness Service
- TRiM 3rd Party Risk Management
- DataG Data Governance Service
- iDAC Identity and Access Management Services
- KVKK+ Personal Data Protection Law Compliance Services
- Fraud Risk Management Services
- Cloud Services and DevOps Solutions
- About Us
- Blog
Türkçe
OUR SOLUTIONS
Pentera
Pentera , which sets out with the slogan “Don’t assume, verify”, provides a significant achievement in the field of information systems security. Pentera simulates real-world threat scenarios and constantly evaluates the organization’s defenses against these scenarios. Pentera proactively detects security vulnerabilities, configuration errors and other vulnerabilities. Thus, it prevents attackers from exploiting these problems before institutions can fix them. It does all this in an agentless and secure way.
PenTera is a platform that automates the verification of security checkpoints and tests , evaluates and reduces corporate cyber security risk. The platform immediately activates a risk-based (CVSS -independent ) remediation roadmap by continuously mimicking real-life attacks and verifying the effectiveness of defensive controls . Able to run on the cloud or locally, Pentera offers security teams an agent-free approach that gives them full visibility into attack surfaces and security gaps .
Pentera’s usage scenarios include verification of security checkpoints , automated penetration tests, risk-based vulnerability management , applications and MITER ATT&CK compliance . The platform continuously improves cyber resilience by increasing the efficiency of cyber security teams and reducing response time, while also directly increasing the effectiveness of the security program by reducing false positives and modeling attacker behavior.
Pentera offers multiple protection measures and performs comprehensive, reliable testing to ensure the secure design of security programs while strengthening organizations’ cybersecurity postures . The platform reduces dependency and expense on third-party testing while increasing the efficiency of cybersecurity teams .
Pentera is an ASV (Automated Security Validation) solution and also touches other areas of security activity. Pentera offers some values that are different from similar security applications. This comparison is shared in the table below.
Comparison of Pentera with products operating in other fields is shared in detail under the following headings.
Breach and Attack Simulation (BAS) vs Pentera
BAS products perform simple tests to a limited extent . They work with agents and perform playbook-based simulations. At this point, Pentera works with adaptive tests in an area covering all systems without any agency .
Automated Penetration Testing (Automated PT) vs Pentera
Many tools are used within the scope of Automated PT, and most of these tools are non-institutional . Additionally, using these tools requires serious expertise . The use of these tools involves some risks and may result in unexpected effects . Pentera constantly provides ethical penetration tests in a reliable manner that will not harm the systems, without requiring additional expertise.
External Attack Surface Management (EASM) vs Pentera
EASM products discover, monitor and security evaluate institutions’ Internet-facing surfaces . EASM has automatic discovery and security assessment of institutions’ internet-exposed assets . Unlike Pentera , it tests the vulnerabilities of institutions’ online assets and checks the validity of leaked accounts .
Vulnerability Management (VM) vs Pentera
Vulnerability Management is the control of vulnerabilities discovered on a defined group of assets. It also includes remediation efforts specified in the CVE for relevant vulnerabilities . Pentera also checks dynamic vulnerabilities such as password-related security problems that are not included in the CVE database . It also verifies these vulnerabilities in a way that eliminates the possibility of them being false-positive .
Because technological conditions are constantly changing, many processes and understandings are also changing. In today’s conditions , Vulnerability Management is no longer sufficient to meet security needs. At this point, Pentera produces significant value in security problems arising from password security, non-patchable vulnerabilities and configuration errors, where Vulnerability Management is inadequate . With pentest automation , it carries out an ethical test on a wider attack surface with the tactics and techniques defined within the MITER framework . The biggest difference of Pentera at this point is that it performs these tests reliably, without any agency or additional tools .
MITER ATT&CK Today
Pentera maps test results onto the MITER ATT&CK framework and is fully compatible with MITER ATT&CK . This feature is invaluable to security professionals. Mapping a completed test result both as an attack map (kill-chain) containing vulnerabilities and on MITER ATT&CK, which includes techniques and tactics , contributes greatly to the evaluation study.
Pentera supports single or distributed deployment architectures. It does not require pre-establishment and does not require agents . Pentera consists of the following components.
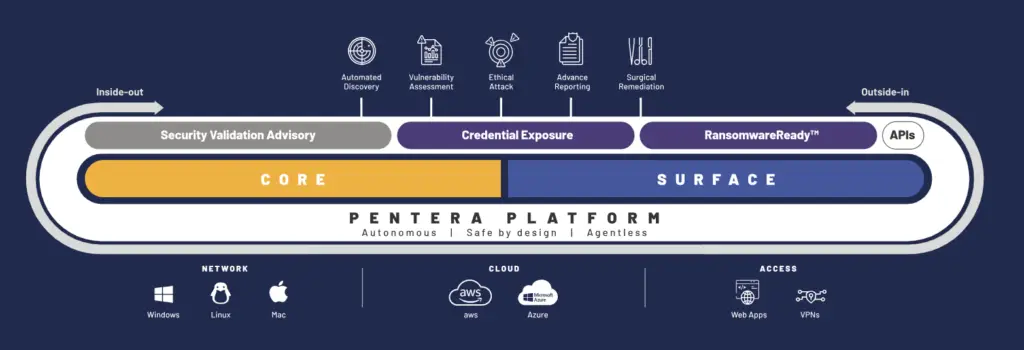
Pentera Core
It is a module that works on the internal network of institutions . Continuously performs security verification with safe and ethical attack tactics, techniques and procedures (TTPs) . It is the main platform that performs all functions of Pentera within the organization .
Pentera Surface
It determines the external attack surfaces of institutions and performs security verification in line with attacks aimed at seizing assets open to the internet . The external attack surface consists of institutions’ assets open to the Internet , attack vectors related to these assets, and vulnerabilities belonging to these assets . These assets are domain names, digital certificates, operating systems, servers, IoT devices and network services . Pentera Surface works as software-as-a-service.
Pentera RansomwareReady
It checks the maturity and effectiveness of organizations ‘ security defenses against popular ransomware attacks . The module covers a range of ransomware attacks and performs tests similar to real-life attacks . It performs these tests completely safely without damaging any system . Thus, the efficiency and effectiveness of security applications within the institution are measured .
Credential Exposure
It performs security verifications using accounts belonging to institutions leaked in environments such as open web, deep web and dark web . Compromised accounts are a very serious security problem for institutions . These accounts are used in attacks such as hijacking other accounts, infiltrating institutions, data theft or ransomware . Pentera collects these leaked accounts and allows institutions to easily track them. In addition, it checks the validity of these accounts by testing them on different attack surfaces .
Security Validation
Pentera is a platform aimed at increasing the usage capabilities of its users .
Pentera first initiates a discovery process to identify targeted assets in the specified organization . It then uses different techniques to take over accounts and gain authority . It then continues its infiltration and exploitation actions with lateral movements . Pentera decision-making system has a model similar to human intelligence . Although its attack model is rule-based, it manages itself dynamically and constantly updates its attack models . Can act with an intuitive and pragmatist understanding, like a security expert doing pentesting. It acts as a standard user to bypass systems such as EDR, NDR, IDS, IPS and EPP .
In line with the “Safety By Design” principle, Pentera does not have a negative impact on the business continuity and assets of institutions . All tests are carried out smoothly with security and control mechanisms .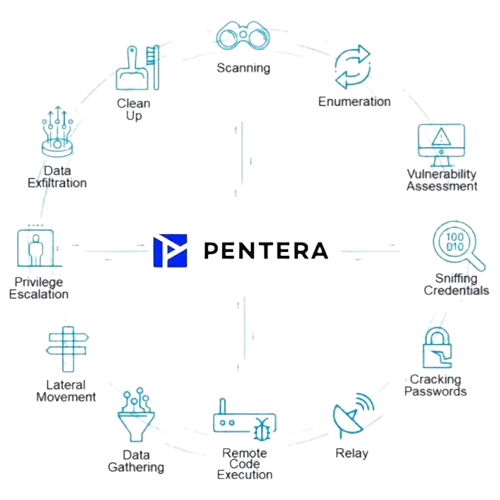
Some Features and Advantages of the Pentera Platform
- Comprehensive Cyber Security Tests : Pentera tests cyber security vulnerabilities in depth. By imitating real cyber security attacks, it effectively reveals companies’ security vulnerabilities and provides guidance for improvements.
- Effective Risk Assessment : The platform strengthens the security posture of institutions by evaluating and prioritizing security risks. This helps organizations improve their risk-based approach.
- Automation-Powered Validation : Pentera automatically verifies the effectiveness of security controls. This reduces the workload of security teams and allows them to continuously improve their security posture.
- Wide Scenario Coverage : Offers a wide range of usage scenarios, from security controls verification to automated penetration tests, from purple team applications to MITER ATT&CK compliance.
- Advantages over Competitors : Pentera reduces false positives and directly increases the effectiveness of cyber security programs by modeling attacker behavior. These features give Pentera an advantage over its competitors .
- Easy Integration and Use : With cloud-based or local installation options, Pentera can be easily integrated and used. Its agent-free structure provides flexibility and convenience to security teams.
The Pentera Platform plays an effective role in solving the challenges faced by institutions in the field of cybersecurity. It provides protection against cyber threats by optimizing the detection and response processes for security vulnerabilities. Pentera increases the efficiency of security teams, reduces costs and takes an important step in creating a safer cyber environment.