- Our Solutions
- Our Services
- ASSESS Cyber Risk and Maturity Assessment
- AWARE Cyber Security Awareness Service
- TRiM 3rd Party Risk Management
- DataG Data Governance Service
- iDAC Identity and Access Management Services
- KVKK+ Personal Data Protection Law Compliance Services
- Fraud Risk Management Services
- Cloud Services and DevOps Solutions
- About Us
- Blog
Türkçe
” Being accessible to the outside world opens the door to unpredictable Cyber Security events, as mentioned in the Black Swan theory . “
Cybersecurity has always been a toothache that keeps organizations up at night. When we look at the IT components, there is the hardware at the bottom, the hypervisor or container on top, the operating systems on top, and the exciting world of applications on top of that. As a matter of fact, these applications do not fit into the small world of the operating system and are exposed to the outside world . At this point, a concept that upsets everyone comes into our lives: Cyber Security. Of course, there are security approaches in the internal world of institutions, but the basis of the general understanding of security lies in self-protection against the outside world and external threats. Nowadays, everyone from all walks of life, from all ages, will have to deal with cyber security one day. Every mortal with a smartphone, robot vacuum cleaner or carplay needs a minimum of security awareness. So why?
These systems have a common feature: Internet ( Internet Connected) . When internet connection is involved, we find ourselves in an unknown like the Aztecs . The Internet is actually an individual’s or institution’s gateway to the world. So how safe is this world ? Of course, opening up to the world is not a rhetorical statement . We’re talking about being accessible to anyone from Zanzibar to Guinea . You may become a target by an attacker on the other side of the world. It is also a fact that you may be a soldier working for him through the botnet without realizing it . The issue of cyber security is such a half-real, half-fantasy world. So how likely is this said ? In the Black Swan theory , it is mentioned that events that are fictional in part can happen, even if they are unlikely, and when they do, their impact will be great . Risk calculation is based on probability and impact. Therefore, at the end of the day, even though the probability is low, the result is the same in terms of risk as the impact will be large. In other words, organizations do not experience security breaches every other day, of course, but experiencing this once has such an impact that it turns into a huge incident .
So, if we take a look at the keywords; Cyber Security, Black Swan and the Outside World . So let’s wrap up the situation like a breath taken after a long tirade. Being accessible to the outside world opens the door to unpredictable Cyber Security events, as mentioned in the Black Swan theory . I think this sentence is now more understandable.
Kimin nesidir bu “Exposure Management”
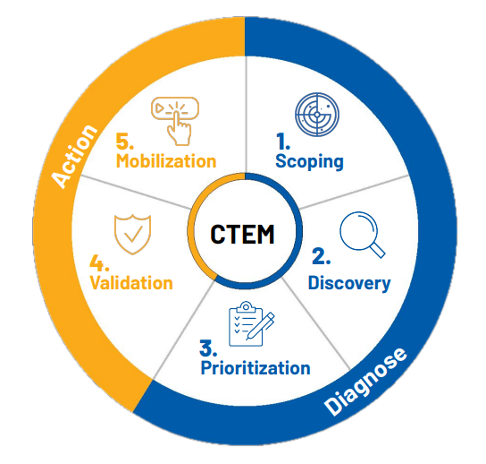
A report called “Implement a Continuous Threat Exposure Management (CTEM) Program” was published by Gartner in July 2022. Accordingly, the CTEM program is expressed as a comprehensive and continuous approach to manage the cyber security risks of institutions. CTEM would create a dynamic line of defense against security threats and enable institutions to be proactive. Therefore, we can consider this not as a technology but as a methodology that disciplines the security posture of institutions. This methodology is described as the framework in the picture below. Thus, the concept of “Exposure Management” quietly entered our lives.
Years ago, when security was mentioned, what came to mind were security patches and authorization management . So, if patches were applied properly and authorization management was handled properly, we were as solid as slate . And if we had spares, it would be delicious . So, could the security regime remain like this for years? Of course no. Let’s go even further back. The concept of security was based solely on the firewall, and this was the entire cyber security concern. As a matter of fact , technology has changed so much that in the blink of an eye, we found ourselves on another planet and we all stared at what was happening. Suddenly, vulnerabilities appeared like the plague in the systems in our pocket, on our desk, in our data center. A new concept has entered our lives: Vulnerability Management (VM). With this, many technologies related to vulnerability management have been included in every institution, large or small. Vulnerability management was scanning the systems of institutions and discovering vulnerabilities. It addressed the vulnerabilities it discovered according to the CVE (Common Vulnerabilities and Exposures) catalog, thus providing information for improvement to eliminate the vulnerability.
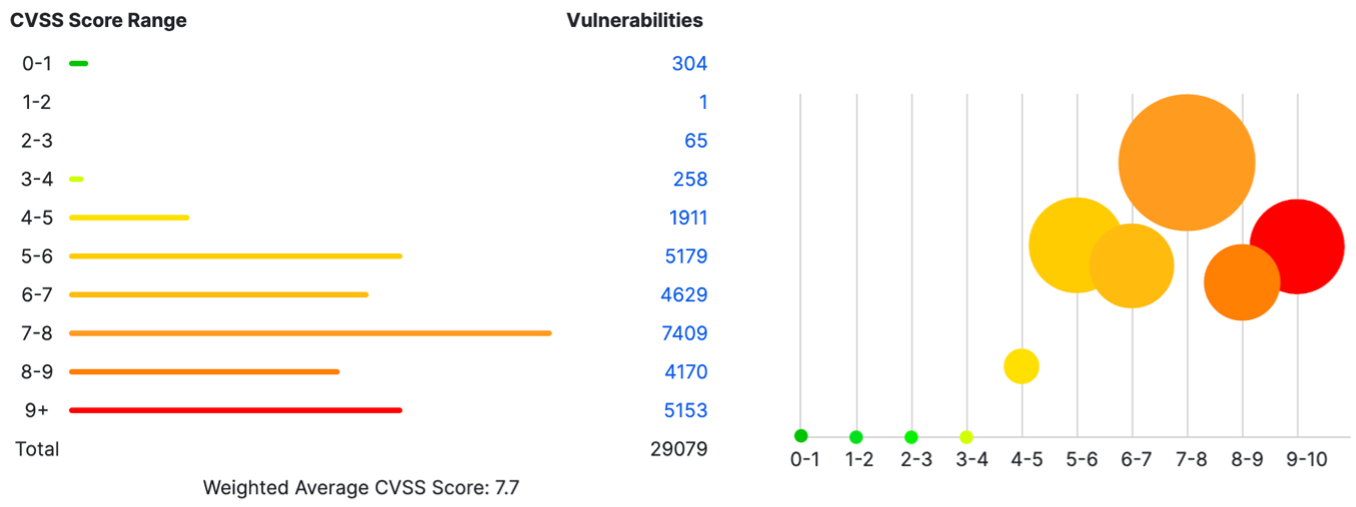
Since these vulnerabilities usually consist of software errors, they are fixed by patch updates. In addition, these vulnerabilities have a criticality value and score (CVSS), which indicates the degree of importance and priority. Therefore, institutions generally create action plans according to the criticality and score of the vulnerability. Vulnerabilities with a score greater than 7.0 (Critical, High) are considered a sign of security problems for institutions and action is taken without delay. Lower scores (< 4.0) are not very interesting and can be ignored.
 Vulnerability Management has become inadequate over time. Because for a vulnerability to be recorded, it must first be discovered by someone. Of course, this discovered vulnerability may have been used by attackers for years. In other words, institutions are always one step behind the attackers, and measures are generally aimed at exposed vulnerabilities. Additionally, “dynamic vulnerabilities” such as configuration errors or weak password usage are not in the field of view of vulnerability management. In vulnerability management, an inventory is basically defined and the presence of vulnerabilities in the CVE catalog is checked on this inventory. Therefore, the vulnerability management approach is inadequate in the dynamism of the exciting world of applications. At this point, the “Exposure Management” approach has emerged to address this inadequacy of vulnerability management. A report published by Gartner predicted that “by 2026, organizations with an Exposure Management approach will be three times less likely to experience a security breach.”
Vulnerability Management has become inadequate over time. Because for a vulnerability to be recorded, it must first be discovered by someone. Of course, this discovered vulnerability may have been used by attackers for years. In other words, institutions are always one step behind the attackers, and measures are generally aimed at exposed vulnerabilities. Additionally, “dynamic vulnerabilities” such as configuration errors or weak password usage are not in the field of view of vulnerability management. In vulnerability management, an inventory is basically defined and the presence of vulnerabilities in the CVE catalog is checked on this inventory. Therefore, the vulnerability management approach is inadequate in the dynamism of the exciting world of applications. At this point, the “Exposure Management” approach has emerged to address this inadequacy of vulnerability management. A report published by Gartner predicted that “by 2026, organizations with an Exposure Management approach will be three times less likely to experience a security breach.”
As of 2023, the number of recorded vulnerabilities is approximately 29,000. 60% of these vulnerabilities have a CVSS score of 7.0 and above, which means that if a policy as mentioned above has been adopted for approximately 17.000 vulnerabilities, urgent action must be taken. Another surprise is that some vulnerabilities are non-patchable. In other words, those that cannot be fixed with a patch and the risk must be reduced. In the report published by Gartner, it is estimated that “by 2026, non-patchable attack surfaces of companies will increase in more than 50% of institutions.”
Another issue that cannot be handled with vulnerability management is passwords. According to research, password reuse is approximately 60-70%. More than 60% of security breaches were committed with compromised passwords. So passwords are still a serious security problem.
At this point, there are a number of applications in the cyber security community that we cannot foresee. These applications, which operate in the following areas, touch several of the CTEM components. Selection of an effective application that completely covers attack surfaces is of great importance in the evolution of institutions’ security approaches from “Vulnerability Management” to “Exposure Management”.
- VM (Vulnerability Management)
- BAS (Breach and Attack Simulation)
- Automated PT (Automated Penetration Testing)
- EASM (Eternal Attach Surface Management)
- ASV (Automated Security Validation)
Unfortunately, choosing the best application for institutions requires making a complicated decision like a prisoner’s dilemma and is a very confusing situation. When we look at each application from its own perspective, we feel the need.
Therefore, we find ourselves in a middle-of-the-road chaos. At this point, “Exposure Management” offers an important perspective to institutions for an up-to-date and permanent security discipline. The CTEM framework is an important reference in determining the solutions needed.
It is said that there is no one hundred percent secure system. Maybe there is a “too good to be true” application that will give us some peace of mind. Who knows…
(In our next article, the fields of activity of cyber security applications will be discussed in detail.)
Resources:
Implement a Continuous Threat Exposure Management (CTEM) Program, 2022, Gartner
Enterprises Must Expand From Threat to Exposure Management, 2023, Gartner
How to Manage Cybersecurity Threats, Not Episodes , 2023, Gartner
Data Breach Investigations Report, 2022, Verizon