- Our Solutions
- Our Services
- ASSESS Cyber Risk and Maturity Assessment
- AWARE Cyber Security Awareness Service
- TRiM 3rd Party Risk Management
- DataG Data Governance Service
- iDAC Identity and Access Management Services
- KVKK+ Personal Data Protection Law Compliance Services
- Fraud Risk Management Services
- Cloud Services and DevOps Solutions
- About Us
- Blog
Türkçe
SecurityScorecard announced that v3.0 scoring will be available in April 2024. Version 3.0 of the Scoring Algorithm is an updated methodology with a scoring relationship based on the probability of a cybersecurity breach.
The company made this scoring feature available to users as a preview in September 2023, allowing users to prepare before this change. Thus, in this period until April 2024, users will be able to evaluate the differences between the current scoring and the scoring v3.0 version.
Developments in SecurityScorecard Scoring Algorithm
-
- The risk scoring algorithm used on the SecurityScorecard platform is changed every 3-4 years.
-
- The total score will now be determined directly by security findings. Currently, it is the weighted average of 10 factors.
-
- The weight value of the factors will be removed. Factors will have scores in the range of 0-100.
-
- The weight values of security findings will continue in version 3.0 of the Scoring Algorithm. However, weight values have changed.
-
- The relationship value regarding the possibility of a cyber security breach is increased for those below the A letter grade.
-
- Users can access the preview version of v3.0 scoring via the option on the Scorecard Issues page. In this way, they will be able to see the differences between the current scoring method and the scoring v3.0 version.
Differences of Version 3.0
The new scoring method includes many important changes.
-
- In Scoring v3.0, the total Scorecard score will directly reflect the security findings detected by SecurityScorecard on companies’ systems open to the internet. Current scoring is based on the weighted average of 10 factor scores.
-
- In Scoring v3.0, factors will no longer have weight values. Factors will have scores in the range of 0-100. Weight values of security findings will continue to be used. In this case, the aim is to make the scoring more understandable and clear.
-
- Security finding types have different severity levels and score impacts compared to the current scoring method. For example, the severity level of using an application version containing a vulnerability is “Information” according to the current scoring method, but in the v3.0 version the severity level is determined as “High”.
-
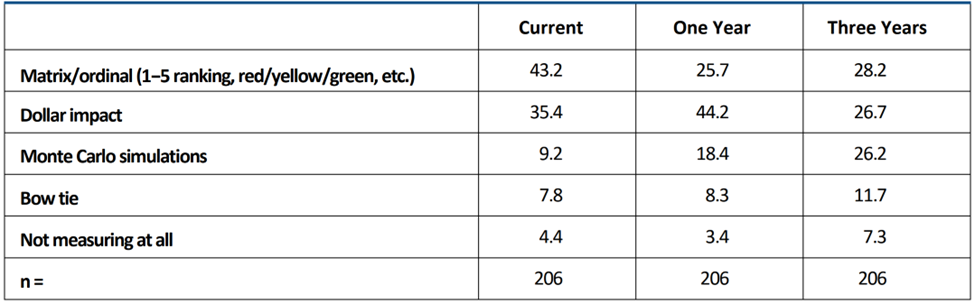
- In the scoring v3.0 version, scores below the A letter grade have a higher probability of cyber security breach association value. It is shared in the table below.
| Not | Probability of violation event based on current rating | Possibility of breach incident in version 3.0 |
| A | 1x | 1x |
| B | 2.6x | 2.9x |
| C | 4.3x | 5.4x |
| D | 6x | 9.2x |
| F | 7.7x | 13.8x |
How to Prepare for Version 3.0?
When switching to scoring v3.0, scores may change significantly depending on security findings on Scorecard. Therefore, it is important to evaluate security findings according to their priority by using the preview feature before April 2024. For this, the following steps are followed.
-
- Scorecard -> Issues -> Scoring 3.0 Preview
-
- Differences in the severity and score impact of security incidents in the current method and version 3.0 are observed.
FAQ (Frequently Asked Questions)
Why did SecurityScorecard change its scoring method?
First of all, changing the scoring method provides a significant improvement in predicting cyber security breach. Additionally, the new scoring method is more understandable to users. In the changing and developing dynamics of cyber security, using methods that reflect current situations is very important in managing cyber security risks.
How often does the scoring method change?
It changes every three or four years.
How will Scoring v3.0 affect historical score data?
The historical score page will include scoring v3.0 data after the scoring v3.0 version transition. It will not affect the score data for the current situation.
What is the scanning frequency in Scoring v3.0?
The scanning frequency is the same as the current version. Scanning frequency varies depending on the type of security finding. Generally, weekly scans are performed.
Which of the two scores on the platform (Current and v3.0 Version) should be taken into consideration?
Elimination of security findings increases the total score for both methods. However, the impact of security findings on the total scoring varies depending on their severity.
Will resolving security findings on the scorecard improve both scores (Current and v3.0 Release)?
If the security findings on the scorecard are resolved, both scores appear to increase. However, the increase in scores may not be the same depending on the impact of the safety findings.
If you would like to manage the cyber security risks of your institution and the third parties that provide products and services to your institution, we kindly ask you to fill out our form to get information about the TRiM service we can offer.